Pfsense
pfSense patches contributed by the kitz community
The following patches have been created to work on pfSense version 2.7.0. They are added or amended as Custom System Patches in the System Patches package on pfSense, there is information about this below the list of patches.
- Remove Schedule from Firewall GUI and also replace Queues with Limiters
- Improved Limiters information page layout
- Only cycle services on IP change IPv4
- Only cycle services on IP change IPv6
- Add Bash shell as option to console/terminal login menu
- Mute web UI access log for cleaner logs
- Firewall page default to LAN instead of WAN
- Compact the Traffic Total page
- OpenVPN page default to client, Traffic shaper page default to limiters
Note adding these patches with the instructions provided wont activate the patch, system behaviour is only changed after clicking apply for that patch, and can be reverted any time. Auto apply defaults to off, meaning they wont be applied on system updates.
Click here for pfSense 2.6.0 patches
To use patches on pfSense you first need to install the System Patches package, this can be installed in the following way.
1 - First login to pfSense.
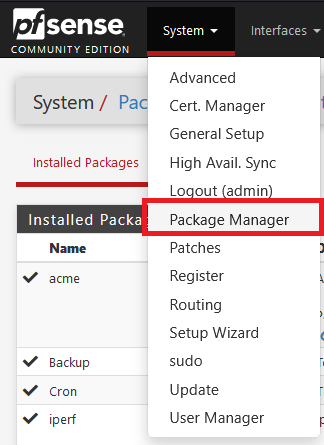
2 - Second click on the System pulldown menu on the top bar and select Package Manager.
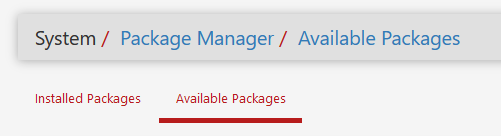
3 - Select Available Packages.
4 - You should see a list of packages appear on the screen.
5 - Scroll down to the System Patches package and then click on the green install button on the right.
![]()
![]()
6 - After a delay the package should be installed.
Now with the System Patches package installed there wont be any patches installed by default, this package just facilitates easy patch management.
The interface can be accessed first by clicking the System pulldown menu again, then by clicking patches on the menu.
At this point there will be two boxes.
The top box will be titled Custom System Patches.

The bottom box will be titled Recommended System Patches for Netgate pfSense® software version 2.6.0.
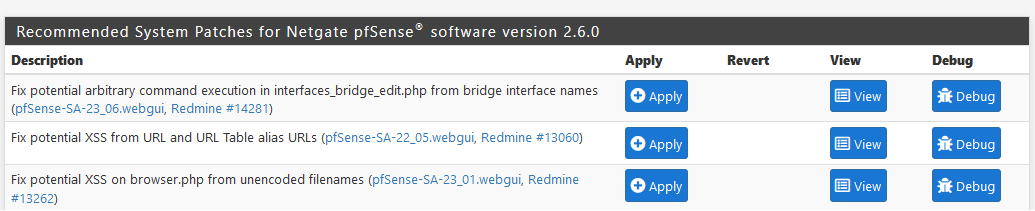
The bottom box is akin to hotfixes. These patches are made by contributors to pfSense code and are things that will be patched in the next release of pfSense. But have been deemed important enough to backport to 2.6.0 via a hotfix.
To install any of these recommended system patches, you just need to click the blue Apply button, they can be safely reverted by clicking the blue Revert button. The blue View button allows you to view the patch code, and the blue Debug button confirms if the patch applies cleanly or not.
One patch in this section might be considered especially useful called Disable pf counter data preservation to temporarily work around latency when reloading large rulesets, this patch will prevent network drops during any firewall rule reloads.
Now on to user contributed patches.
The top box mentioned earlier titled Custom System Patches works similar once a patch has been added, it will have the same blue buttons, and the same failsafe's notably patches that dont apply cleanly will not have the option to be applied.
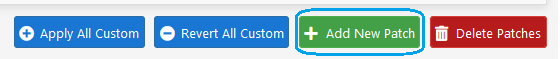
To add one of the patches linked to in this wiki or to make your own patch, there is a green button labelled Add New Patch.